The Privacy Awareness Week, held from May 25 to 31, celebrates the Filipino’s data privacy rights in today’s digitally connected world. Join the National Privacy Commission in protecting the Filipino’s personal information without compromising free flow of information by ensuring your business is compliant to data privacy laws.

Below is a list of important things your business should implement to safeguard your customers’ personal information:
1. Regularly conduct Privacy Impact Assessments (PIAs)
Protecting your consumers’ delicate personal information is not a one-time activity. For one, some of their personal information such as mobile number and address might change. Another reason is some customers might want to restrict the information they have shared a year ago. Hence, your business should have privacy impact assessments done regularly.
A privacy impact assessment or PIA helps ensure that your business has a systematic way of protecting data through implementation of up-to-date data protection and security standards. It also helps you identify areas of vulnerability that may be exploited or abused to gain access to personal information of your customers.

Privacy impact assessments can also help you limit your exposure of liability in the event of data breaches. For example, PIAs often have a checklist of questions such as “Is the personal information you are about to collect really necessary in order to carry out the service to be rendered to the customer?” and “How does your business store the data it collects?” among other things.
For example, imagine your business has 90% transactional sales, meaning these are often one-time purchases. In this scenario, is it mandatory for your business to gather customers’ personal information? If the products they purchase will be shipped to their home or office address, the answer is yes — but you can limit the scope of the damage in the event of a data security breach. You may only opt to get the necessary information such as first name, last name, contact number, and shipping address.
Regularly conducting PIAs make sure you only collect and process useful personal information that you really need, protecting your consumers’ data and fostering their trust in your brand.
2. Keep physical documents containing customers’ personal information in a secure location
It goes without saying that your employees need to be mindful of data leaks anytime your business prints a hard copy of customers’ personal information. If it is really needed to keep copies of physical document, make sure they are kept in a secure location. Implement the needed precautionary measures to protect documents that contain confidential information, and enjoin your employees to properly and regularly dispose of such physical documents in the event they are no longer needed to prevent them from ending up in the wrong hands.

For example, your organization can prohibit employees from bringing these documents outside of office premises. In the event there is a need to bring it outside of the office, make sure your business has the right protocols in place to ensure these documents are returned properly afterwards, such as a logbook that employees can sign when borrowing and returning documents.
This way, it will also be easier for your business to do its internal investigation in the event pieces of information from these documents get leaked. Better yet, it will instill a sense of accountability within your employees.
3. Implement encryption, hashing, and other data security protocols for sensitive digital data
If your business uses IT systems such as a Customer Relationship Management (CRM) platform, make sure that proper security protocols are followed. Implement the principle of least privilege, which limits the users’ access to data based on their user roles. For example, your internal users who serve customers in Manila should only see customer data in Manila. They should not be able to see customer data in Visayas or Mindanao. The principle of least privilege ensures data is only accessed by those who need access to it.
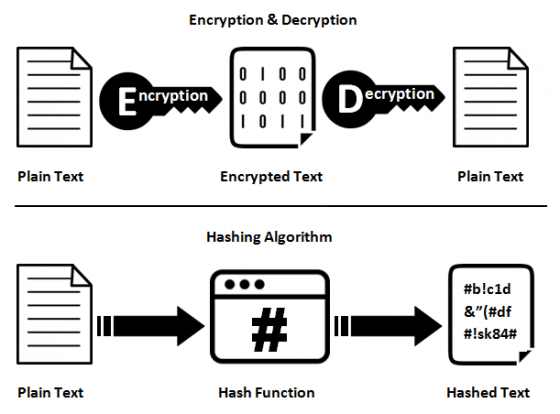
Ensure passwords and other sensitive information are hashed or encrypted so as not to compromise data in the event of a security breach. Encryption and hashing are two functions of cryptography that make it difficult for data to be read and used by attackers. Hashing the string “ABC123” will convert it into a random sequence that cannot be reverted to its original form, while encrypting is a reversible action ideal for transporting sensitive data. This will help secure the flow of information and protect against possible cyberattacks.
Using data protection and security best practices will enable your business to stay compliant to data privacy laws. One such best practice is deploying a demilitarized zone or DMZ. In computer security, a DMZ is an extra layer of protection from possible external attacks on your organization’s internal network. This is especially important if your business consumes third-party application programming interfaces (APIs) or need to provide third parties access to limited data within your internal network.
4. Appoint a Data Protection Officer
This one is really a no-brainer because this is one of the legal requirements for businesses and organizations to be compliant to the Data Privacy Act of 2012. Make sure to appoint a data privacy officer or DPO with the relevant skills on data protection, information security, and industry best practices on cybersecurity as well as knowledge on relevant privacy policies.
The DPO will help ensure your business is and will remain to be compliant to privacy laws and policies and will serve as the point person for anything related to data privacy concerns. Furthermore, the DPO will also be considered as the internal police of the organization when it comes to data privacy matters.
As such, the DPO must have extensive knowledge of the Data Privacy Act, its Implementing Rules and Regulations (IRR), and other pertinent policies. They will be responsible for cultivating data privacy awareness within the organization and to encourage an iterative approach to improving data privacy and security measures and countermeasures.
5. Prepare a response and recovery plan
No matter how careful your organization is, there is the constant threat of data security breaches. This is the reason it is very important to prepare a response and recovery plan. In the event of a security attack or breach, your organization must have a set of protocols to follow to limit the damage of the breach and to stop it altogether.
Your organization’s data privacy officer, in coordination with your information and cybersecurity teams and with the overall guidance of your Chief Information Officer, must come up with a data breach response plan that will identify potential vulnerabilities, list of action items to ensure these vulnerabilities are protected against security attacks, and a list of responses in the event there will be a security breach.

They can also train their IT personnel to respond to breaches and conduct vulnerability and penetration testing to ensure that all computing systems that the business uses are protected from possible security attacks. More importantly, regularly doing these vulnerability and penetration testings can help spot weak points before they are exploited.
Join the celebration of Privacy Awareness Week by ensuring these 5 items are all taken care of in your business. If you need to know more about data privacy best practices, visit this page for more of our articles on Data Privacy.
SOURCES:




